There may have been a time when an annual employee training program on cybersecurity was enough to satisfy regulators that an advisory firm was taking the threats of hackers and other malicious actors seriously.
No longer.
The Securities and Exchange Commission has made no secret that it expects more from firms in the area of cybersecurity, identifying the issue in its recent exam priorities letters, conducting sweep exams focused on firms' cyber policies and procedures, and, most recently, announcing the establishment of a dedicated cyber unit.
TD Ameritrade recently launched a campaign to promote the message to its registered investment advisers that a strong, dynamic cybersecurity training program is an essential element of a modern practice. A key part of that effort is the notion that employee training must be ongoing, that policies to protect the firm's systems and information aren't just a set-it-and-forget-it proposition.
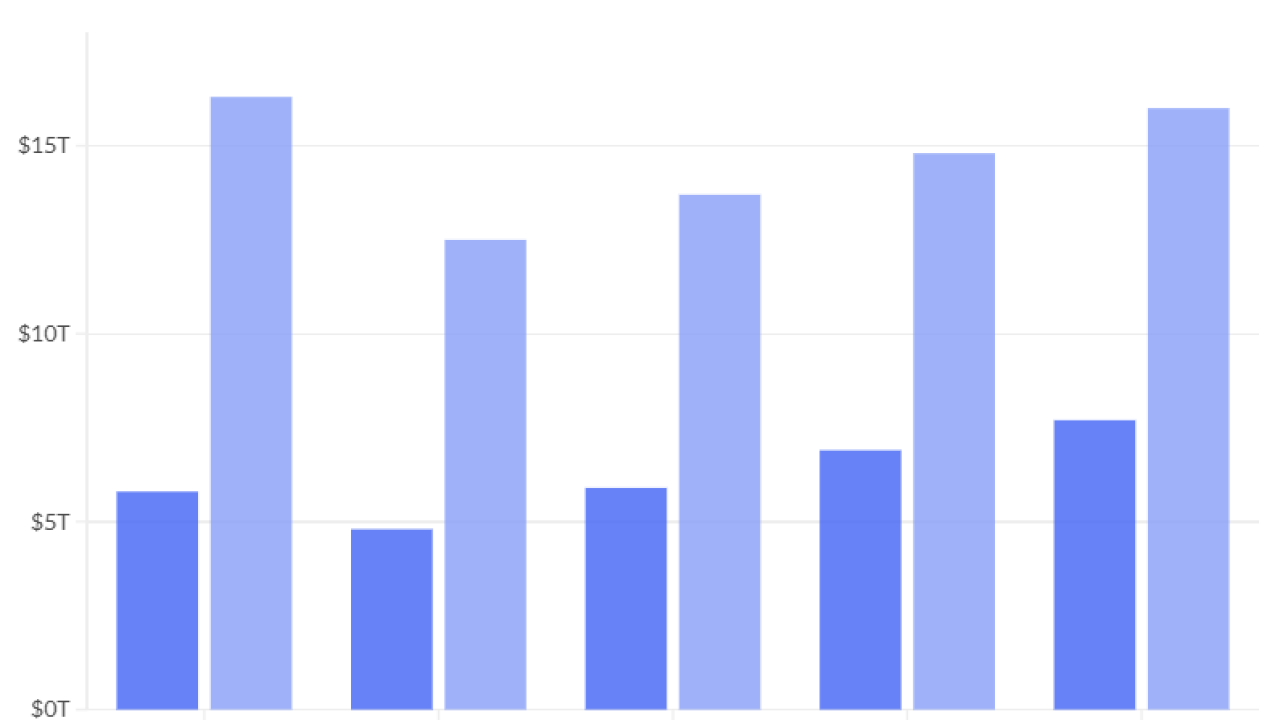
Equifax's data breach may be the most serious, given that it covered 143 million consumers and involved reams of confidential information, but it wasn't the largest. Following are the biggest to date.
“You don't just train the people when they first come in," says Bryan Baas, director of risk oversight and control at TD Ameritrade Institutional. "You've got to keep it fresh in their minds."
Baas also stresses the importance of documenting the firm's policies and procedures governing things such as the proper use of equipment and accessing sensitive systems through mobile devices.
Firms have made a "significant amount of progress in the area, which is great, but from a training perspective it can't be word of mouth, it has to be documented," he says.
"That's going to be the cornerstone of your training,” Baas says.
At CAPTRUST, a large RIA headquartered in Raleigh, North Carolina, Chief Technology Officer Jon Meyer describes his firm's approach to cybersecurity training as one of "recency and repetition," where his team continuously devises new methods to keep employees on their toes to guard against potential intrusions.
For instance, CAPTRUST partners with a vendor to send out fake phishing emails to employees at the firm, attempting to replicate the increasingly sophisticated and polished messages that actual hackers send out in the hopes of gaining entry into a system or obtaining sensitive information. Meyer has also been known to co-opt an employee in one of CAPTRUST's remote offices to leave a USB drive, which when loaded with malware can be an easy entry point into a firm's systems, lying around in the break room. Then if an employee takes the bait of a phishing email or plugs in the USB device, that becomes a training opportunity.
"I think all of those things help us produce a polite yet skeptical employee who is less susceptible to social engineering and other forms of attack," Meyer says. "It really starts with smart employees who learn to be a little skeptical."
Those guerilla tactics supplement CAPTRUST's more formalized training efforts, such as the courses and certifications offered through the firm's learning management system, as well as the ongoing "lunch and learn" sessions where employees receive updates on emerging cybersecurity threats and trends.
Those types of sessions, in addition to providing ongoing training, can have the added benefit of helping employees come to understand why certain policies are in place at the firm, including some restrictive protocols that, without an explanation, could simply be seen as a nuisance.
"It's not just a what, it's a why," Baas says. "Your policies will be much more effective and you have a greater likelihood that your employees will remember them if you explain the why."
This story is part of a 30-30 series on savvy ideas on modernizing your practice.