The stern words of a former FBI agent planted the idea for this month’s issue on cybersecurity. At last year’s FSI OneVoice conference, Clyde Langley, a former agent who’s now vice president of Schwab’s fraud prevention and investigations unit, told a room of worried executives that hackers were probably lurking in their firm’s systems.
“Criminals are sitting in compromised accounts, watching traffic and seeing what you and your clients are talking about,” Langley said.
“Use code words or phrases with each client,” says Financial Planning contributor Donald Jay Korn.
That thought has stayed with me ever since. But when I spoke with Financial Planning Managing Editor Suleman Din about probing this topic more deeply, he opened my eyes to an even more insidious — and lesser-known — digital threat.
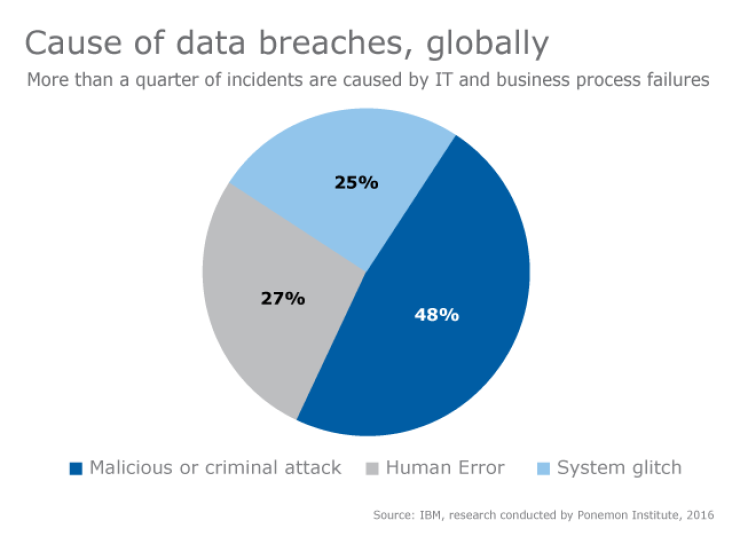
Well-intentioned advisers have been integrating as many new tech tools into their practice as they can, Din told me. But few realize that these programs, primarily built by third-party vendors, could come with glitches and bugs that allow client and firm data to be accessed by thieves, or just mistakenly disseminated by users.
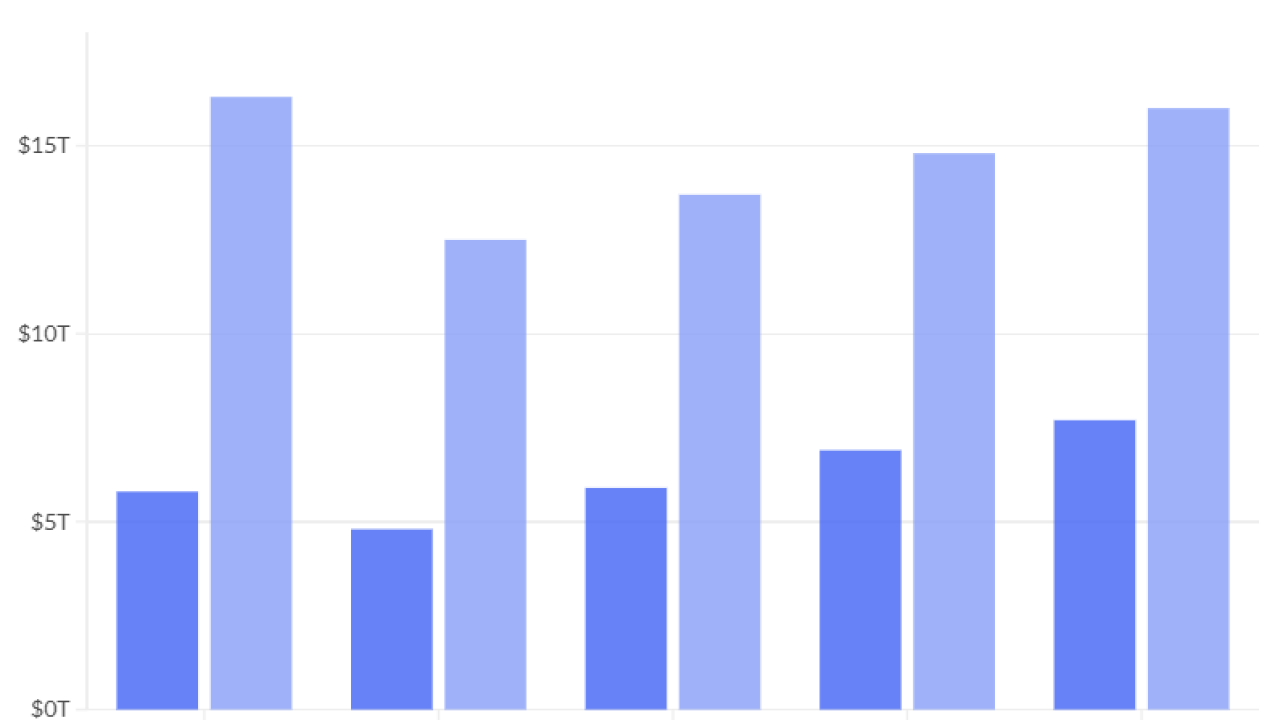
From fiduciary to robos to marketing: A close look at advisers’ top concerns and how their budgets have changed year-over-year, from TD Ameritrade’s annual survey.
Who’s responsible for the resulting data leaks? Advisers. Not vendors.
“It’s a regulatory and legal issue with real consequences for advisers, who shoulder the blame and fallout even if the firm didn’t cause the data breach through any action of their own,” Din says.
-
What breakaway brokers and service providers can learn from the collapse of Sanctuary Wealth Services.
January 26 -
A consortium of fintech companies have formed a new industry group to advocate for better data sharing via open APIs.
January 19 -
Advisers have been warned: SEC's exam guidance to focus on cyber threats and issues involving seniors, leaving little excuse for noncompliance.
January 13
“Advisers have to take an invested, proactive approach to learning about the tech that they are using and the partners they choose,” Din adds. Stay on top of security inquiries, he warns, but expect a runaround. He says he was surprised by how “vendors can thwart diligence inquiries from advisers and still get business.”
Donald Jay Korn, who wrote a companion piece on cybersecurity, tells me his research revealed ways to stop thieves from using information from already-breached systems.
“Require a live phone call instead of an email, for instance,” he says. “Use code words or phrases with each client, and mandatory delay times to verify a cash request,” Korn adds, citing his source, Sanjiv Bawa, founder of Chi Networks.
Those are words that should stick with you, similar to the FBI agent’s warning that stuck with me.